Companies should never try to intercept their users' encrypted


7 important tips for email security you don't want to miss
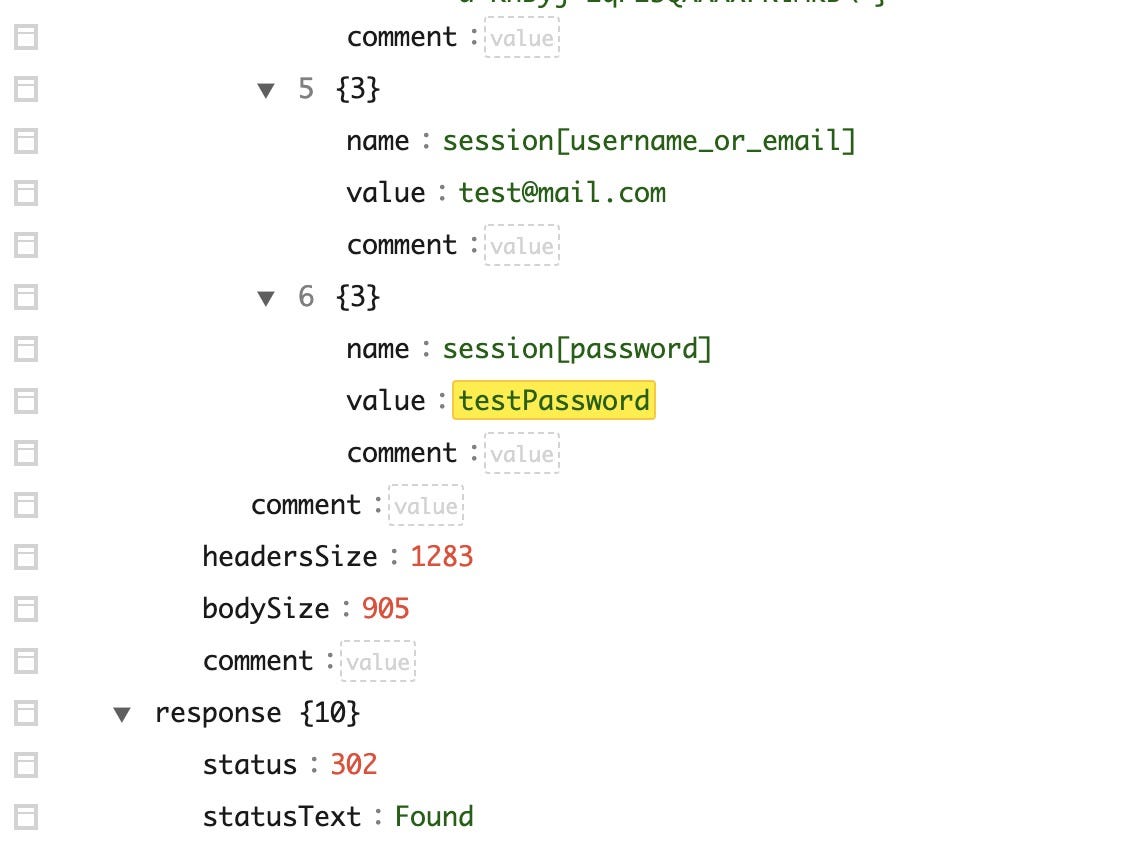
Intercepting plaintext credentials of HTTPS traffic from popular login sites (Microsoft, , Twitter, Google etc), by Aaron Garcia

Zoom Meetings Do Not Support End-to-End Encryption

Securing web browsing: protecting the Tor network

8 Ways to Prevent Replay Attacks — How to Stop the Interception and Retransmission of Data
WhatsApp Backdoor allows Hackers to Intercept and Read Your Encrypted Messages

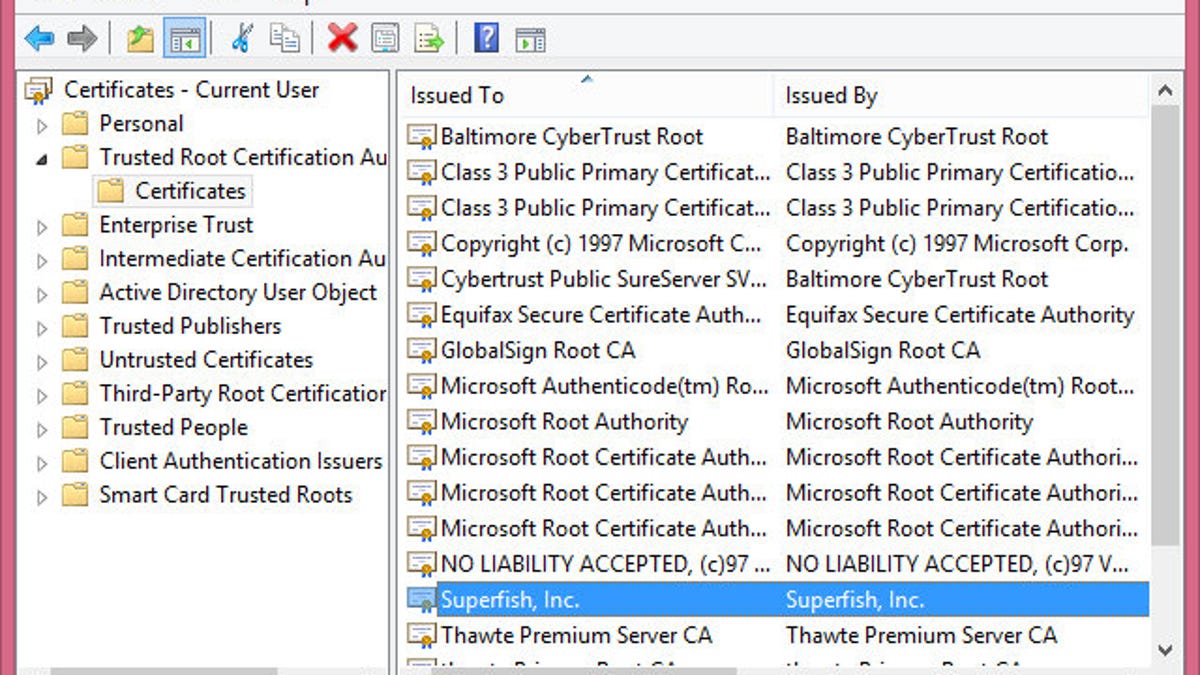
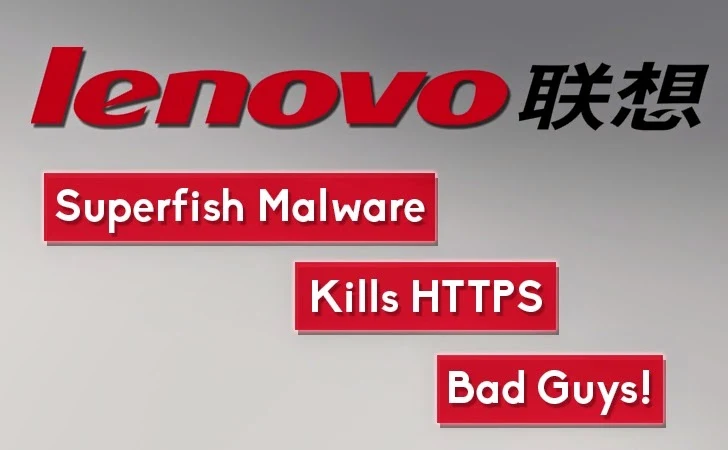
Risks of Installing a Trusted Root CA on Your Device

Cybersecurity 101: Everything on how to protect your privacy and stay safe online
:max_bytes(150000):strip_icc()/how-to-keep-your-debit-card-transactions-safe.aspx-Final-0c92611f34934a92bcc0e2e86fa6b1fc.jpg)
8 Rules to Keep Online Debit Card Transactions Safe

THE USE OF ENCRYPTED COMMUNICATIONS BY CRIMINALS